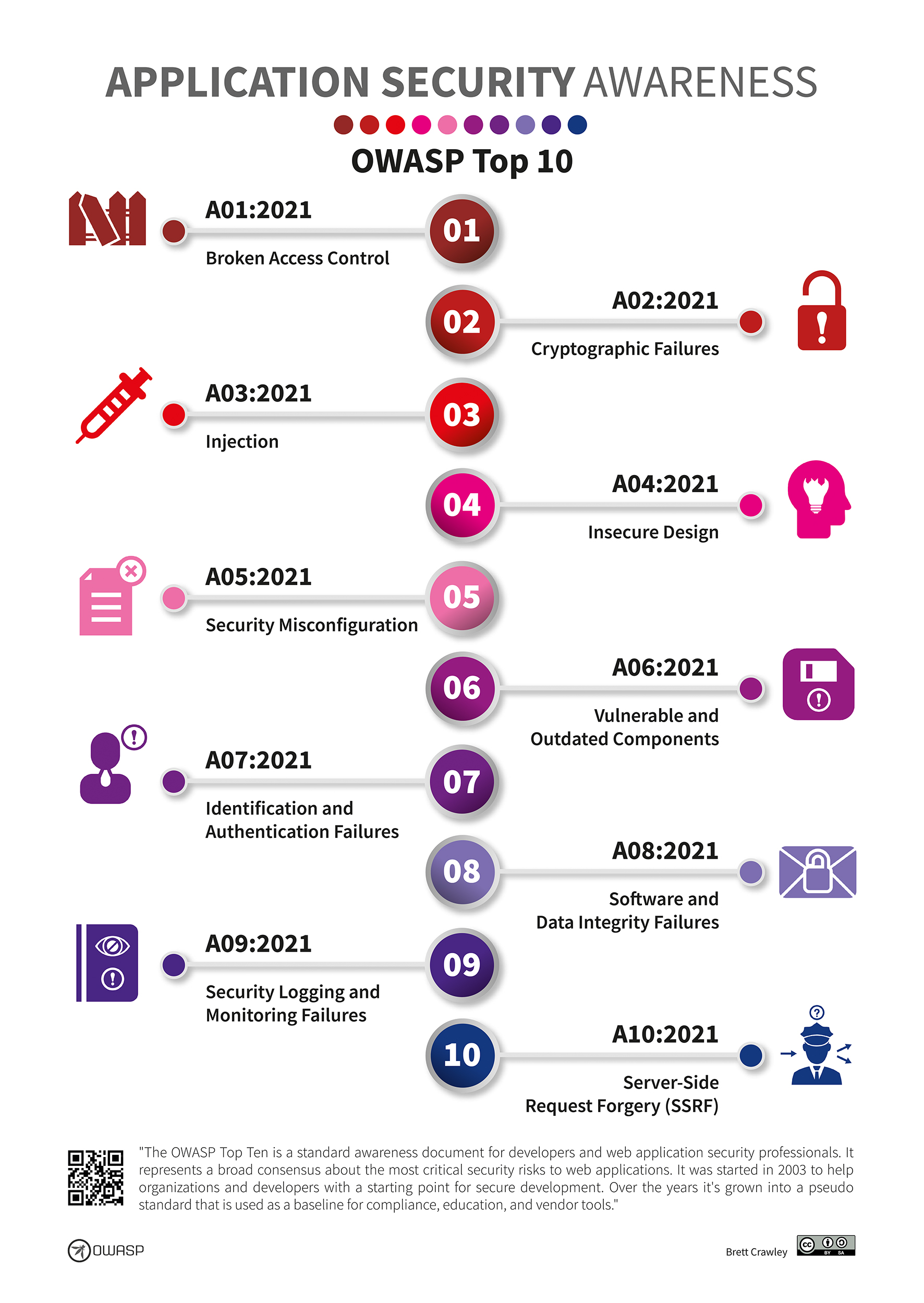
Prepare for the OWASP Top 10 Web Application Vulnerabilities Using AWS WAF and Our New White Paper | AWS News Blog

GitHub - OWASP/Nettacker: Automated Penetration Testing Framework - Open-Source Vulnerability Scanner - Vulnerability Management https://www.secologist.com/



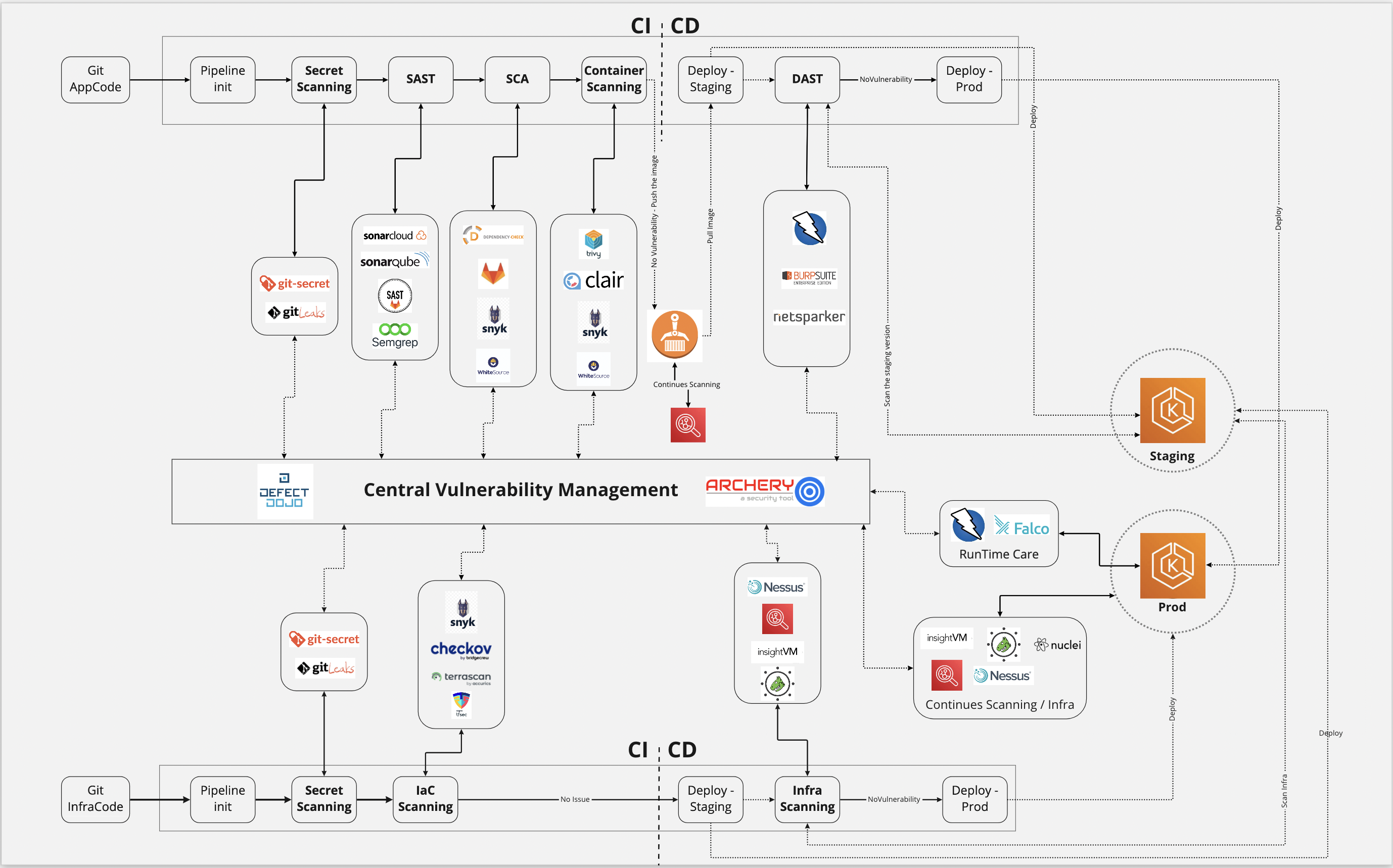

.png)